Dev Sentinel Story 2: Architecting Dev Sentinel - Evolving AI Agent Failures into Reusable Experience
Architecting Dev Sentinel: Evolving AI Agent Failures into Reusable Experience
In Part I, I explored the philosophy of “Struggle Equity”: how failures and missteps are the raw materials of senior engineering intuition. AI coding agents like Claude Code iterate at lightning speed, but they lack this long-term architectural intuition.
An agent can retry a flawed architectural approach multiple times across different sessions without ever accumulating pattern awareness. It treats every ModuleNotFoundError or infinite recursion as an isolated incident.
This presented a unique system design challenge: How do we capture an agent’s failure, structure it, and evolve it into a reusable architectural signal without polluting the agent’s reasoning?
Dev Sentinel is the architectural answer to that question.
1. The Architectural Problem of Agentic Workflows
The core challenge with AI coding agents is their lack of persistent architectural memory. While they excel at solving isolated problems, they struggle with recognizing recurring anti-patterns across sessions.
An agent might:
- Repeatedly choose the wrong concurrency model for IO-bound tasks
- Apply the same flawed abstraction pattern in different contexts
- Miss environmental constraints that caused previous failures
Each failure is treated as a fresh problem, with no accumulated wisdom to guide future decisions.
2. The Core Principle: The “Fresh Session” Isolation
The most critical design decision in Dev Sentinel was intentional isolation.
There is a temptation when building AI wrappers to constantly inject past context directly into the prompt. However, injecting raw failure logs into a Claude Code session creates two massive problems:
- Context Bloat & Token Degradation: The prompt becomes heavy with irrelevant past mistakes.
- Reasoning Bias: The agent becomes hyper-fixated on avoiding past errors, often stifling fresh, creative problem-solving.
Therefore, the core tenet of Dev Sentinel is strict separation: Claude Code must execute freshly in every session. Dev Sentinel exists entirely externally. It acts as an observer and a pattern synthesizer, intervening only when an evolving failure pattern breaches a similarity threshold.
3. System Architecture Overview
To achieve this non-intrusive observation, Dev Sentinel is decoupled into distinct processing layers:
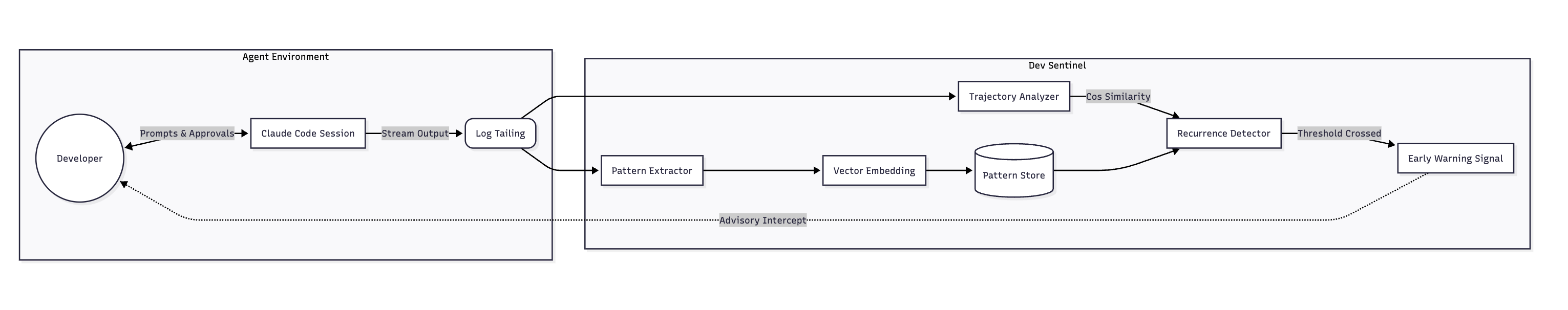
Core Components:
Pattern Extractor: Tails the live session stream. It strips away content-specific noise (like specific variable names) and extracts the structural shape of the failure and the tool invocation sequence.
Pattern Store: The long-term memory. Instead of storing raw text, it stores evolving failure abstractions.
Recurrence Detector: Continuously compares the active session’s trajectory against the Pattern Store using vector similarity.
Early Warning Signal: An advisory prompt surfaced to the developer—not a hard block on the agent.
4. The “Evolve” Mechanism: From Noise to Signal
The biggest differentiator of Dev Sentinel is that it doesn’t just log errors; it evolves them.
A single failure instance is noise. Repeated similar failures form a signal. Dev Sentinel evaluates patterns along two axes: Frequency (how often it happens) and Generalization (abstracting the specific bug into a structural flaw).
Let’s look at how a data structure evolves inside Sentinel’s storage.
Stage 1: The Raw Failure (Noise)
Initially, Dev Sentinel captures an isolated event:
{
"session_id": "abc123",
"error_type": "ModuleNotFoundError",
"context": "import missing_module",
"resolution": "abandoned",
"confidence": 0.1
}
Stage 2: The Evolved Pattern (Experience)
As the agent encounters similar structural issues across different files and sessions, Dev Sentinel merges these nodes. It increases the confidence score and generalizes the structural trait:
{
"pattern_id": "import-resolution-failure",
"occurrences": 5,
"generalized_context": "dependency import without verification",
"structural_traits": ["missing package", "no fallback", "no error handling"],
"confidence": 0.85,
"advisory": "Consider verifying package installation before import"
}
When enough instances align, Dev Sentinel upgrades the event from an isolated log to a heuristic warning.
5. Design Tradeoffs
Building this required balancing several engineering tradeoffs:
Vector Search vs. Graph Traversal: While a Knowledge Graph could perfectly map code dependencies, vector embeddings were chosen for the Recurrence Detector. Embeddings are much faster at catching “fuzzy” similarities in agent intent (e.g., recognizing that tweaking a timeout and increasing a retry limit are structurally the same band-aid solution).
Advisory vs. Guardrail: Dev Sentinel emits signals, not constraints. Hard constraints reduce the autonomy that makes AI agents useful in the first place. Advisory signals preserve developer agency, mirroring how a senior engineer intervenes during pair programming—not by grabbing the keyboard, but by asking, “Are you sure this is the right abstraction?”
6. The Future of Accumulated Struggle
Agent capability is currently scaling through better foundation models. But eventually, model intelligence will commoditize. When every team has access to the same baseline reasoning, the differentiator will be context and accumulated experience.
Dev Sentinel is an exploration into whether we can externalize architectural intuition. By observing, structuring, and evolving failures, we can turn the inevitable struggles of agentic development into our most valuable engineering asset.
This is Part II of the Dev Sentinel series. In the next post, I’ll dive into the implementation details: how the Pattern Extractor works, the vector similarity algorithm, and the practical challenges of building a non-intrusive observer system.